Stop Using Kernel-Mode WireGuard, For Now
pfSense and FreeBSD to pull kernel-mode WireGuard
WireGuard is a secure network tunnel, which aims to replace IPsec as well as OpenVPN. It’s more secure, more performant, and easier to use.
Well, this past week the kernel-mode WireGuard was pulled from the FreeBSD 13 development entirely.
The code that was integrated into FreeBSD was found to be sub-standard when subjected to post-deployment review.
Security vulnerabilities were found when enabling Jumbo frames.
Netgate host of the pfSense open source firewall project also decided to remove kernel-mode WireGuard.
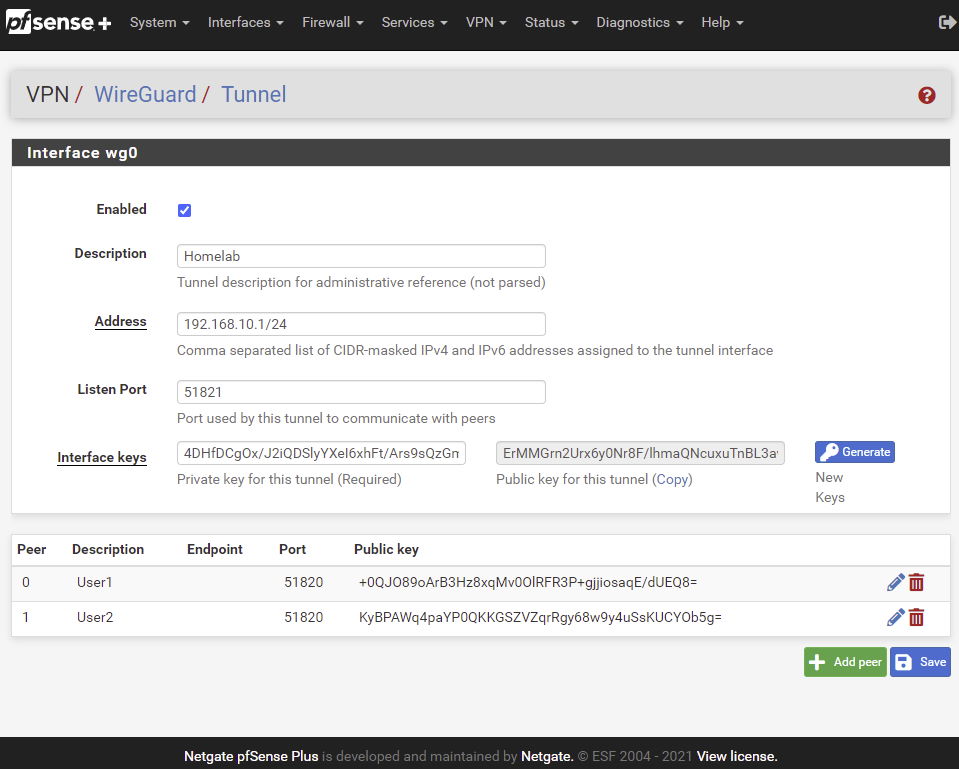
We introduced a kernel-mode version of WireGuard to our most recent pfSense software releases – pfSense® Plus Version 21.02 (which has since been superseded by Version 21.02-p1), and pfSense Community Edition (CE) software version 2.5.0. As noted in a follow-on blog, questions and concerns with the implementation have surfaced that require attention.
Given that kernel-mode WireGuard has been removed from FreeBSD, and out of an abundance of caution, we are removing WireGuard from pfSense software pending a thorough review and audit.
We will follow the FreeBSD developments on kernel-mode WireGuard. Should WireGuard again be accepted into FreeBSD, we will re-evaluate it for inclusion in a future version of pfSense software.
Netgate – Jim Thompson, March 18, 2021
Final Thoughts
I’ve been a pfSense user for many years and been very happy with the project.
I was in the process of testing and recommending this new kernel-mode WireGuard feature of pfSense to others, but now I must wait to see how this develops.
I am still glad to see that the project leaders of pfSense quickly acted and removed this feature once they heard the news.
Why I think pfSense is still the best firewall.
It is still safe to use WireGuard in FreeBSD, but when using the user-mode version of WireGuard (wireguard-go). It’s a little less performant than the kernel-mode, but it’s stable.



