What Is Phishing And How To Protect Yourself
What Is Phishing?
Phishing is the fraudulent attempt to obtain sensitive information, such as usernames, passwords, credit card details, by pretending to be someone trustworthy.
Typically done through emails & texts, phishing often directs users to enter personal information on a fake website that look and feel like the legitimate site.
You often see phishing emails that pretend to be your bank, social media, streaming services, online stores (Amazon, Ebay, etc…).
The message often tells a story to trick you into clicking on a link or opening an attachment. They include things like:
- saying they’ve noticed some suspicious activity or log-in attempts
- claim there’s a problem with your account or your payment information
- say you must confirm some personal information
- attach a fake invoice
- want you to click on a link to make a payment
- say you’re eligible to register for a government refund
- offer a coupon for free stuff
Types Of Phishing
There are various types of phishing that can be more sophisticated. They all have the same goal, to trick you into giving sensitive information.
Spear phishing – This is when the phishing attempt is direct to a specific person or company.
Whaling – Another phishing attempt to a specific person, but specifically at senior executives and other high-profile targets.
Catphishing – Is an online deception that involves getting to know someone closely in order to gain access to information.
Clone phishing – This is where someone gets access or sees your email, then makes an almost identical copy pretending to be from the same person. They claim to be responding or continuing a email conversation, but are trying to trick you into giving information.
Voice phishing or vishing – When you get a voicemail claiming to be from your bank. The message tells you to dial a phone number in regard to problems with your account. Once you dial this number, you are prompted to enter your account and PIN.
SMS phishing or smishing – Is where a text message is sent to your phone, where the message uses one of the methods above to trick you into giving out your personal information.
Examples
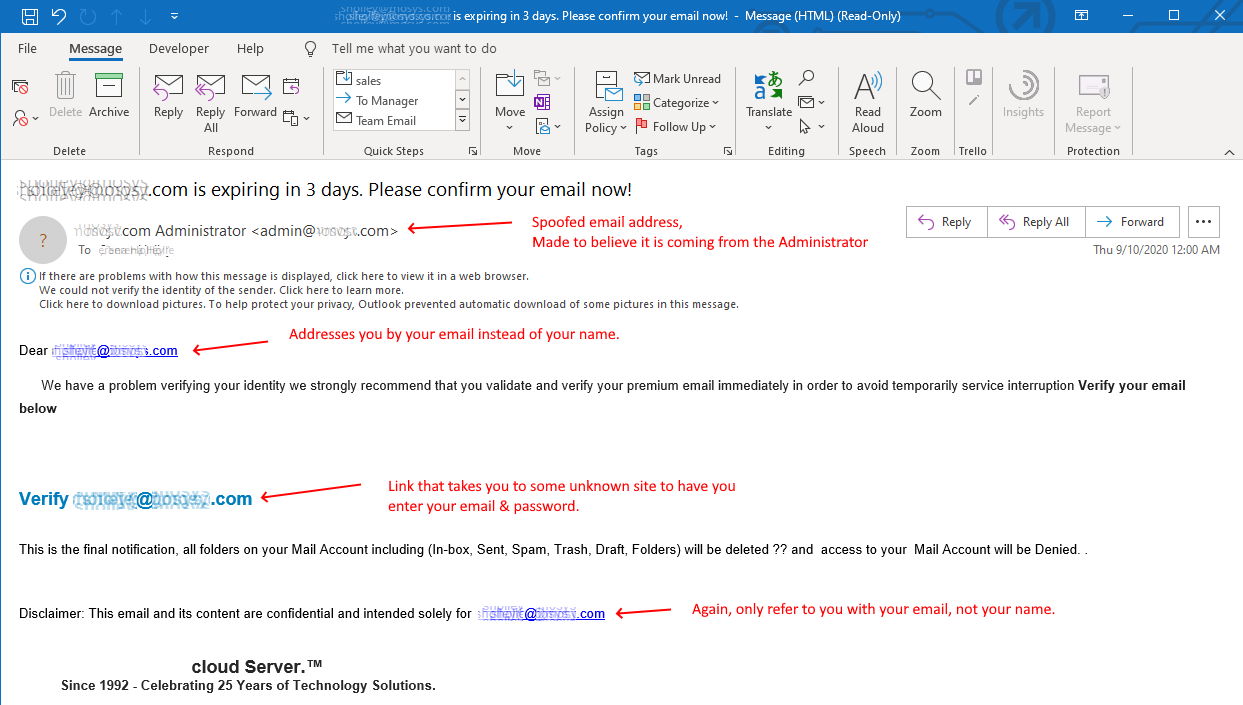
First example is of an email that tries to appear to be coming from the Administrator of your company or email service.
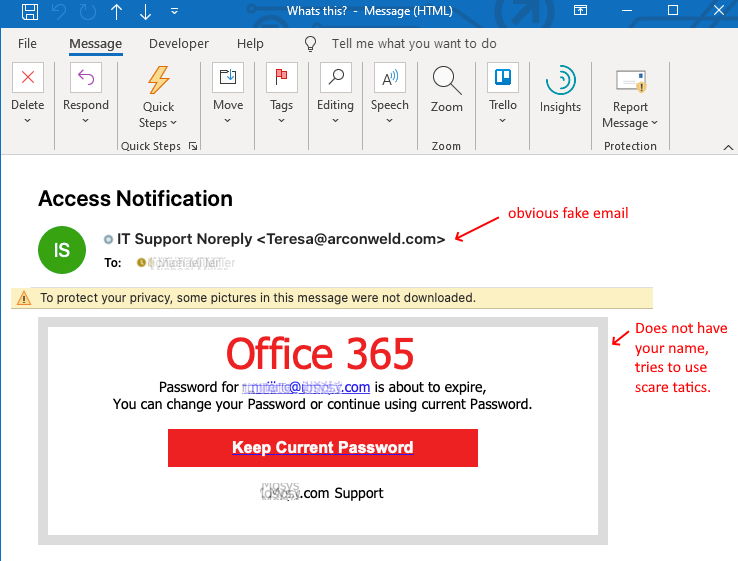
Second example is trying to impersonate Microsoft’s email service.
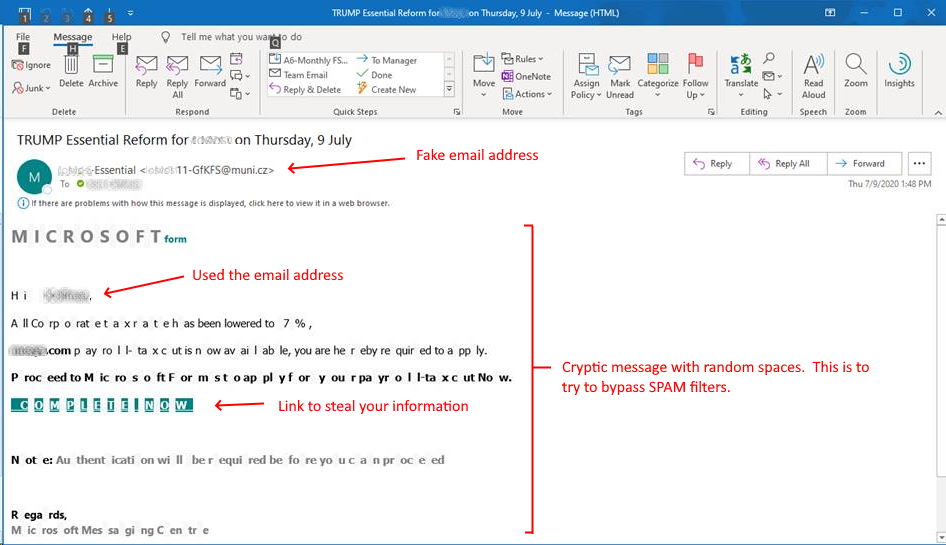
Third example is using cryptic text, so that to make it less likely to be flagged as SPAM or Junk.
How To Protect Yourself
Learn to recognize phishing scams
- When you get an email, are you expecting this email?
- Look at the From: and To: address fields in the email. Verify that they look valid.
- Does the message content look funny?
- How does it address you at the beginning of the message? If they address you by your email, like: “Dear youremail@email.com”, then they obviously don’t know you.
- Are there misspelling and typos? How is the grammar and is the tone appropriate?
- Do the links take you to some unknown website? Never click on links in emails. If you hover your mouse over a link, it will display the URL at the bottom of the browser or in a pop up box. Again, do not click on it, just move your mouse over it to see the URL.
- Never open attachments unless you absolutely know it is safe.
- Assume all emails are scams until you prove they are valid.
- Even when you think an email is safe, don’t click on links. You should open a separate browser window and manually go to the website.
What To Do If You Responded to a Phishing Email
If you think a scammer has your information, like your social security, credit card, or bank account number, go to IdentityTheft.gov. There you’ll see the specific steps to take based on the information you lost.
How To Report Phishing
You can report phishing attacks to the FTC at reportfraud.ftc.gov. Click on the Report Now button to start the process.